In this write up I’ll be exploiting 2 different vulnerabilities to create a single outcome – changing the secret message of the default BWApp account – Bee.
I will be using CSRF (Cross Site Request Forgery) within an IFrame injection to achieve this.
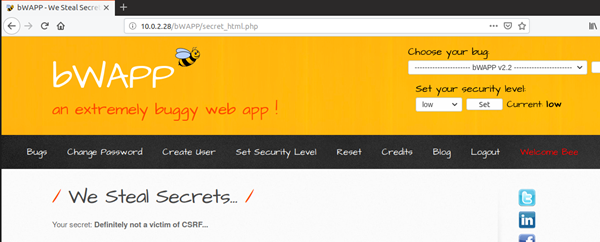
To start let’s take a look at Bees secret message on my Ubuntu machine. Bee is definitely not a victim of CSRF yet.
Next I made a BWApp account on my Kali machine called ‘pentest’ – I wanted to be sure that I had exploited the vulnerabilities properly.
Once I had a new account I tested the form that changes the secret message, this is located at BWApp/csrf_3.php
To test the form I used BurpSuite as a proxy to capture the requests that the form sends.


The ‘secret’ parameter changes the secret message, the ‘login’ parameter is the user who’s secret will be changed, and ‘action’ executes the change. I used this information to create a new HTML form which I will be injecting as an IFrame shortly.
I want ‘bee’ to be unaware that they have triggered this change so I have created the form in a way that it automatically submits when it loads using
<body onload=”document.forms[‘FORM NAME’].submit()”>

I saved this form on my attacking machines web directory and visited the BWApp page that is vulnerable to IFrame injection – /iframei.php

I changed ParamUrl to the location of the HTML file I created earlier and changed the width and height of the IFrame to 0, this should hide it from view.

Afterwards I used bitly to shorten the URL, further hammering home the advice – don’t just click on any old URL you see!

At this point let’s just pretend I sent this URL to bee in an email or something and cleverly social engineered them into clicking it.
I opened the URL on my Ubuntu machine.

The IFrame page loads and there is nothing on it – perfect.

Navigating back to bees secret phrase…

To summarise one user of a website has successfully changed the information of another without their permission, the implications of this kind of attack are clearly huge, especially if the account compromised is an admin account, this could potentially give an attacker full control of the system.