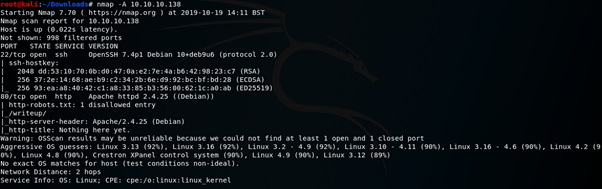
An initial port scan using nmap reveals SSH running on port 22 and an Http sever running on port 80, interestingly there is a robots.txt entry disallowing the directory – /writeup.
Visiting the webpage reveals that there is a DOS protection script in place but there is potential for false-positives, so any bruteforcing is off the cards. It also reveals an email address which will hopefully be useful later – jkr@writeup.htb

I navigated the /writeup directory that robots.txt informed me of in my port scan, this brought me to a page with write-ups for hackthebox machines. After scanning the pages for information I used Wappalyzer to examine the technology used on the page, CMS Made Simple was interesting.

Searchsploit revealed a lot of exploits for CMS Made Simple, one of the most recent was an SQL Injection exploit which had a python script to it.

The script is simple enough to use, I only have to supply a URL and by choice – a wordlist to crack any passwords that the injection might find.

I used exploit.py –u http://10.10.10.138/writeup –crack -w /usr/share/wordlists/rockyou.txt
This provided me with a username and a password – excellent! I used these details to login to machine via SSH as the user – jkr

With access to the machine I downloaded pspy64, this allowed me to monitor activity on the machine.

This revealed that whenever an SSH connection was made a script called run-parts was executed.

The path shows that the first place that will be checked for scripts in an undefined location is /usr/local/sbin. The command find / -type d –writeable 2>/dev/null reveals that I can write to this directory.
I navigated to this directory and created a file named run-parts with the command su root

I logged out and back in via SSH which triggered the script successfully, but didn’t escalate my privileges; it did however prove that I was on the right track and the script was being run as root (UID=0)

I edited the run-parts script to create a reverse connection back to my machine.

I then set up a listener on my machine and repeated the earlier steps, this awarded me with a root shell!
