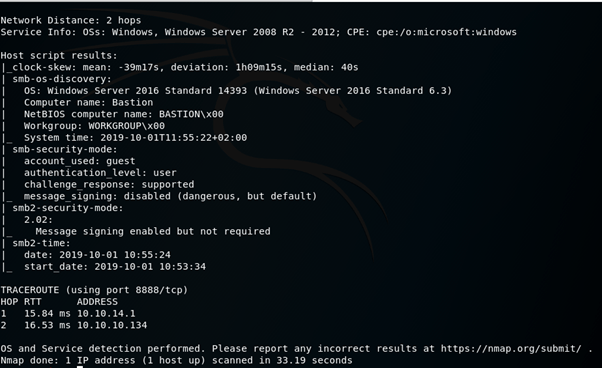
A port scan using nmap reveals the machine has an SMB share that is accessible using the guest account.

I used smbclient to take a look at what was being shared.

Backups looked interesting so I decided to dig a little further into that.

This eventually lead me to a directory that was storing VHD files (virtual hard disk) which I presume are backups of the machines hard drive.

In order to read the contents of these backups I need to somehow mount them, I found a great article explaining just how to do this.
https://medium.com/@klockw3rk/mounting-vhd-file-on-kali-linux-through-remote-share-f2f9542c1f25
I followed the instructions and eventually had access to the files on the disk.


Coincidentally, not long before I attempted this box for the first time I was curious about cracking windows password hashes and did some reading up on it, this prepared me nicely for the next steps.
I navigated to the System32 config directory, the files that I’m interested in here (SAM and SYSTEM) can’t be accessed whilst the OS is running, but because this is a backup the OS isn’t running so I can access them.

I copied these files to a folder on my desktop ready to be cracked.

I passed these files to a piece of software called samdump2 and outputted the results to a file called hash.txt

Next I cracked the hash using the ever helpful John The Ripper, revealing L4mpje’s password as bureaulampje.

I then used these credentials to log in via SSH.

After some enumerating I eventually found some software called mRemoteNG, some googling revealed that this program is used for remote connections and it stores hashed passwords in its config files which are easily cracked. The config files in question are usually stored in /Users/*user*/AppData/Roaming/mRemoteNG – which they were.

Reading confCons.xml showed an Administrator account with a hashed password, great!

I read up on decrypting the password and was ready to write a python script to do so, but before I did I decided to check if there was already one out there (work smarter, not harder!) – which there was, called mremoteng-decrypt. I copied the hash into a new file and passed it through the script, revealing a password for the Administrator account.

I used SSH to login with the Admin account.

What a great box with some valuable windows experience!