This is the first of what I plan to be many tutorials on BWApp (Buggy Web App). BWApp is a platform designed with loads of different web vulnerabilities to help security researchers understand different types of attacks and how to mitigate against them, it is heavily focused on the OWASP Top 10, divided into the ten categories with plenty of different subcategories to go at. There is also a security level option for low, medium and high, this will change the way you have to approach the pages, as it will start to make things harder to find and add in things such as character filtering.
I started with HTML Injection, specifically using GET.

I start by taking a look at what the form does by filling First name as “Hack” and Last name as “Me”.

It simply welcomes whoever has kindly provided their details. But does it accept HTML?

By putting HTML bold tags around the name it should display the name in bold if the form is susceptible to HTML injection.

Great! Maybe I can add a new form and capture the details entered into it? I whipped up a quick and easy HTML login form that links back to a listener on an attacking machine.

I used this HTML as my details on the page.
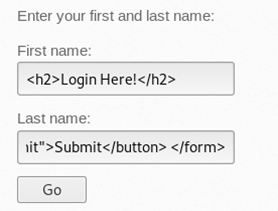
Posting these created another form! Great!

Once the form was active I set up a listener using nc –lvp 2345
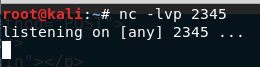
Filling out the form and submitting it should capture the details on my attacking machine.

And it does!

I decided to stop here as I think this proved that the page is vulnerable, however this could be exploited a lot further as the HTML injection is actually part of the URL, and therefore the page could be shared to other unsuspecting users in its current state or even with much more malicious things going on.
This was done on the low security setting, for medium just change the HTML metacharacters for HTML encoding (like what you see where the shell captured the request) and it will work exactly the same!