Level 2 presents us with a new challenge and shows us why XSS can be so dangerous, we’re going to be looking at Persistent XSS. This is when a script is run from user-posted data loaded from the server the page is located on.
In this level the <script> tags have also been filtered so these won’t work (you can try though…), this means we’re going to have to be a little bit smarter about how we inject our script.
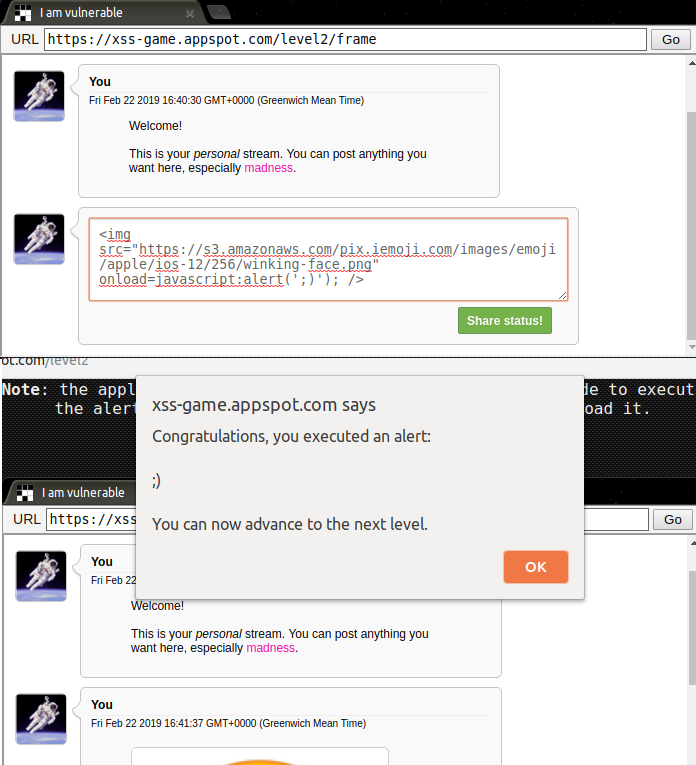
We’re presented with what I presume is some sort of message board. The first message shows the word madness in pink which leads me to believe that HTML is accepted in the form, I wonder if it accepts pictures?

So we’ve established that we can post pictures using HTML, now we need to execute some JavaScript! We can simply use HTML’s onload attribute to build something that looks like this:
<img src=”WhateverYouWant.jpg” onload=javascript:alert(”); />
This basically just tells the HTML to run the alert script whenever the image is loaded.
The other way we could complete this level is by forcing an error and using the onerror attribute.
Every time this page is visited now, as long as that image (or error) is present the script will run, this can obviously cause some serious damage and is a bug that should be treated as such. Basically don’t let people post HTML to your site or at very least make sure that metacharacters are properly escaped.